From MMORPGs to battle royale shooters, it’s fun and thrilling for gamers to immerse themselves in a digital world filled with millions of other players.
Once an online game reaches the highest level of popularity it becomes like a world of its own—with its economy, massive variety of items, and culture. And while most of the dangers and challenges are merely a part of the game, there are also real threats gamers need to protect themselves from.
Online privacy is a hot topic these days. When digital experiences provided by social media, games, and apps exploded in popularity your average person wasn’t ready for the privacy ramifications of it all.
Like most tech companies, gaming companies want to collect data about their customers to improve their games, to better understand what gamers want, and of course to increase profits by selling the data or using the data themselves.
Savvy gamers are now deciding for themselves how much data collection is too much. More than ever, gaming platforms like Steam, PSN, and Xbox Live are giving people the tools to protect their privacy and specify which data they’re comfortable sharing and which data they aren’t.
So, let’s dive in. Here are the things you can do to improve your privacy in online video games.

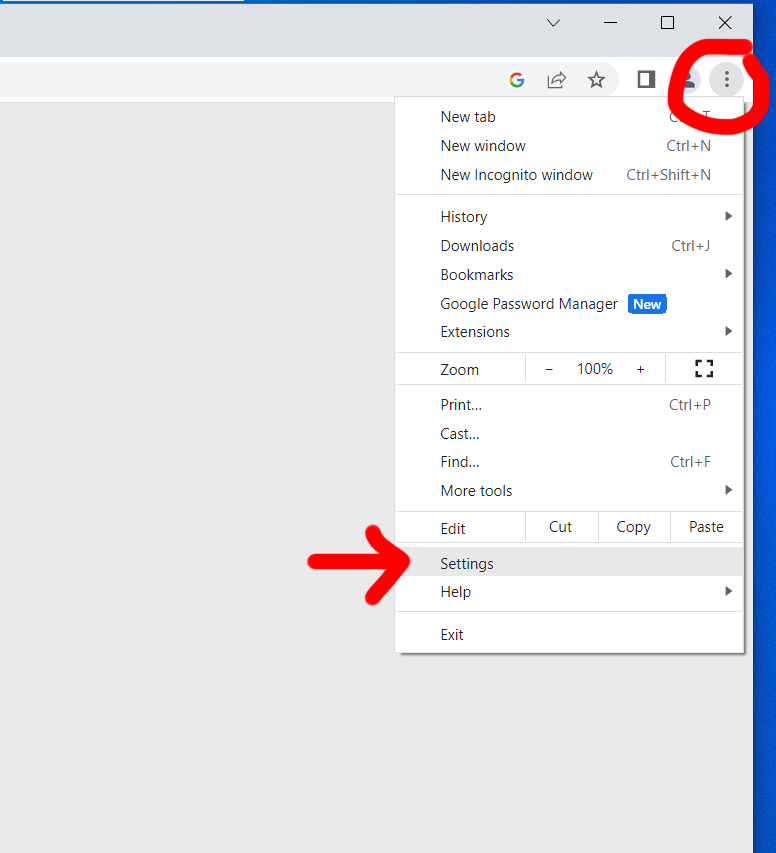
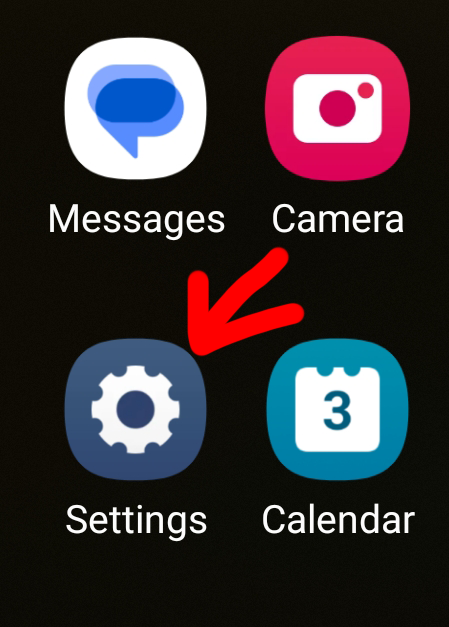
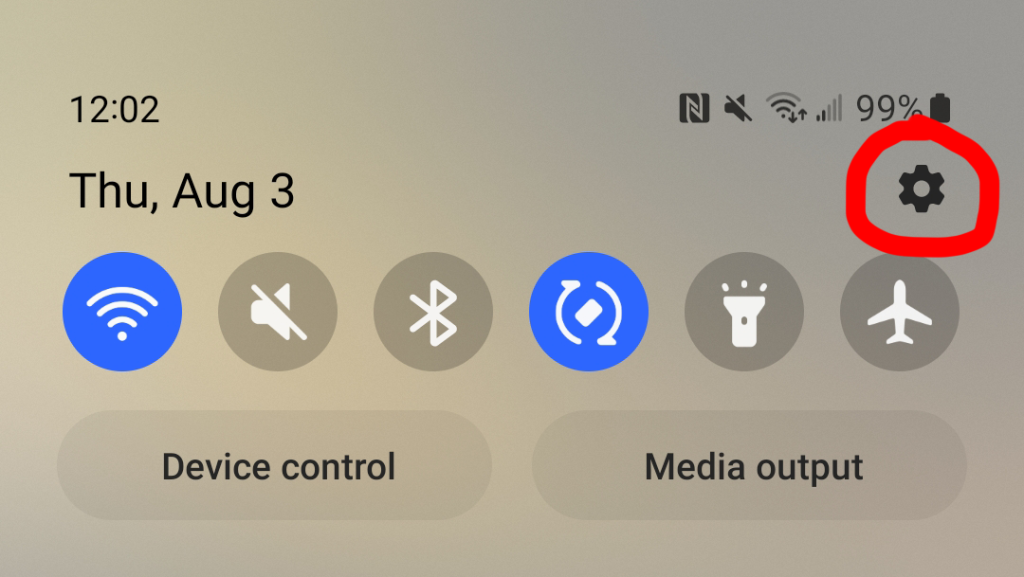
Tweak Your Privacy Settings
When it comes to privacy settings, there’s almost always room for improvement from the default settings.
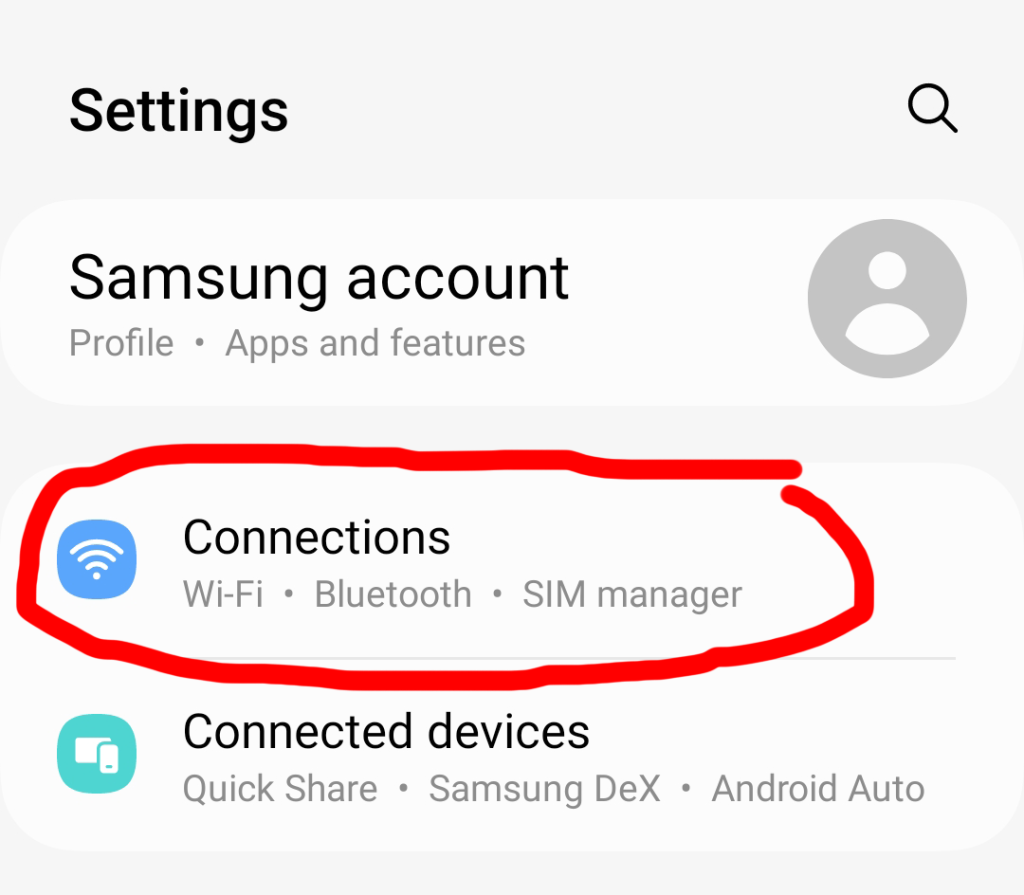
You need to drill down into menus and sometimes make decisions that prioritize either privacy or features and convenience.
Thankfully, once you tackle it, you’re in good shape for years to come until the gaming platform you use overhauls its approach to managing privacy.
To learn how to tweak your game console settings, see LetMeBy’s guide to protecting your privacy on PS5 and protecting your privacy on Xbox Series X/S.
Unlink Your Social Media
Many big game companies such as Blizzard Entertainment and Bethesda Softworks allow their users to connect their social media accounts to their gaming accounts.
It might seem like an interesting feature to explore if you post content about gaming, but linking to social media may grant the game company access to parts of your personal data such as your name, profile photo, or even what you post and in-game conversations.
It’s almost always preferable to log in with a password specific to that gaming account rather than something like Facebook as there is typically a privacy cost.

Keep Your Antivirus Active and Up-to-Date
Good virus protection is always a must on Windows, but for avid online gamers, it’s even more essential.
Some gamers disable their antivirus software to play online or don’t protect their PC at all because they believe it affects performance. Studies have found that in four out of five cases there’s no reduction in frames-per-second (FPS) when playing games with security software running. And in the rare case it has an effect, it’s not a noticeable one.
The hurdle is antivirus software can sometimes launch automated actions that interfere with your gaming experience. Some examples of this are antivirus database updates, notifications of stopped threats, or scheduled hard drive scans.
Choose antivirus solutions that allow you to delay updates and scans while you play games. Some security software such as Kaspersky [Amazon] have a game mode to ensure it doesn’t start using system resources during an intense boss fight.
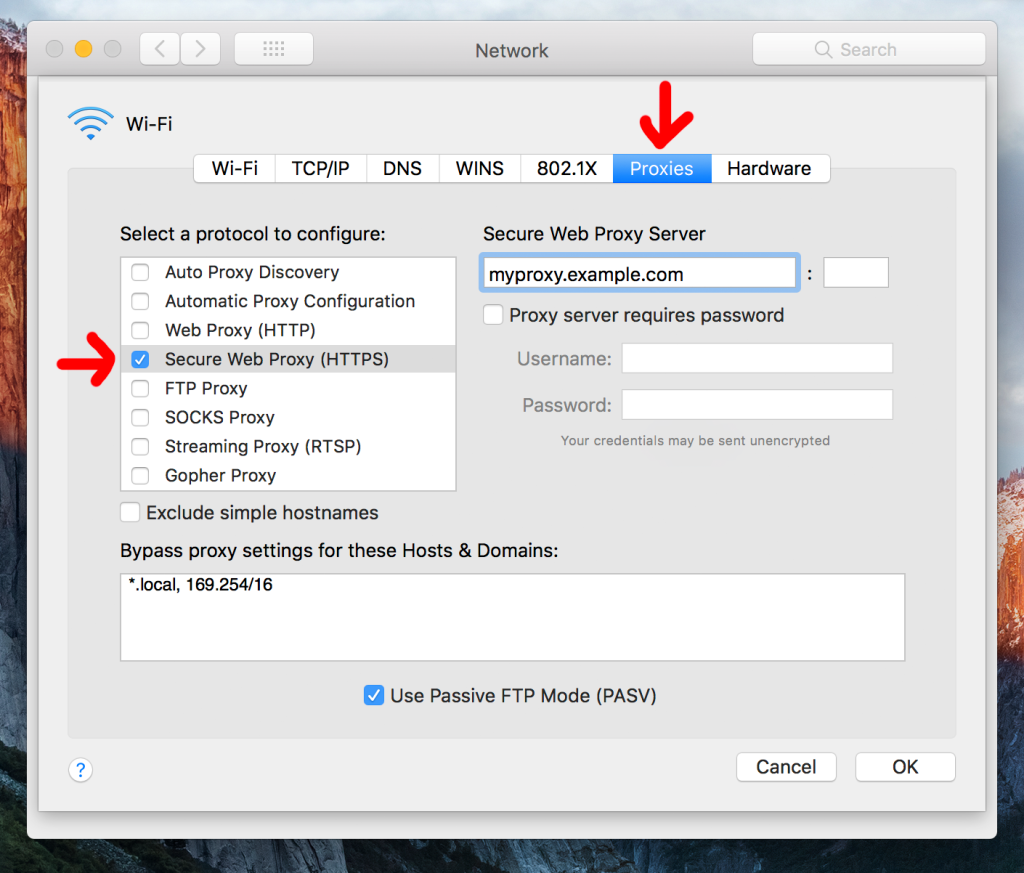
Manually Block Data Collection
The services that collect data about you during a gaming session are stealthy indeed. These processes take place in the background so you don’t ever notice them.
Windows users have the power to block servers from collecting data about them. Open up your hosts file and add the IP address and hostname associated with the service you want to block.
Managing these connections manually requires research and tech skills, but you can’t always achieve the desired effect from the game or platform privacy settings. At times it’s better to take matters into your own hands.
Don’t Save Your Credit Card Info
Gaming platforms and consoles make it easy for people to save their credit card info for future purchases. Simply put, it’s more likely you’ll make purchases if you can do it in a few clicks. And companies like getting those frictionless sales.
While it’s no doubt convenient to have your credit card on file, it has risks that come along with it. If somebody gains access to your account, they could manage to collect your credit card info or even make purchases.
More and more, credit card companies are requiring confirmation that changes to your card are genuine. However, it’s still best to play it safe and enter your card info each time you shop for new games.

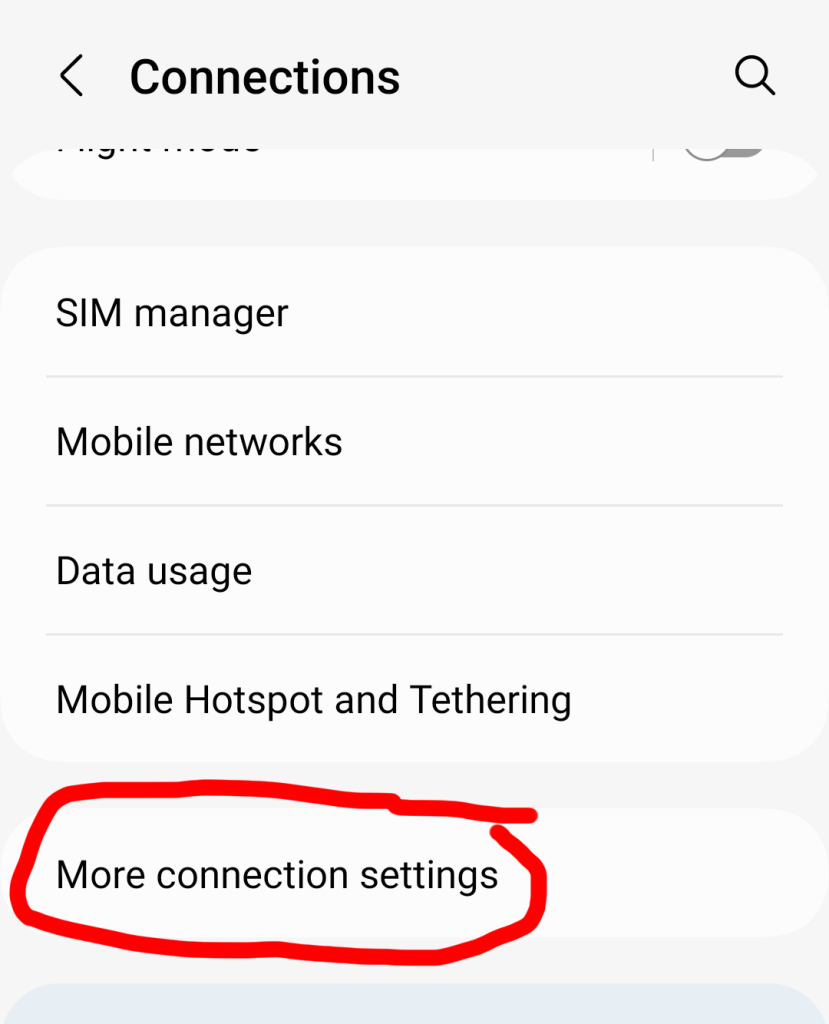
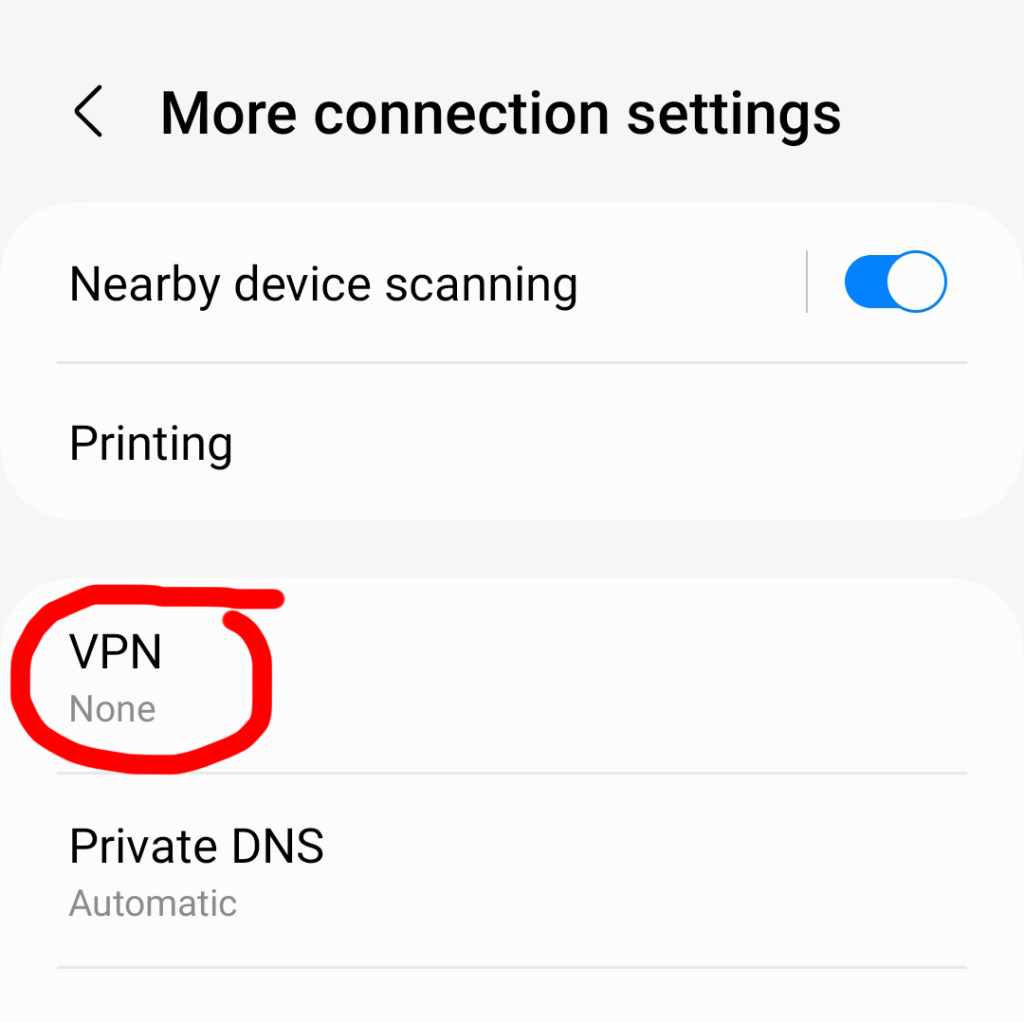
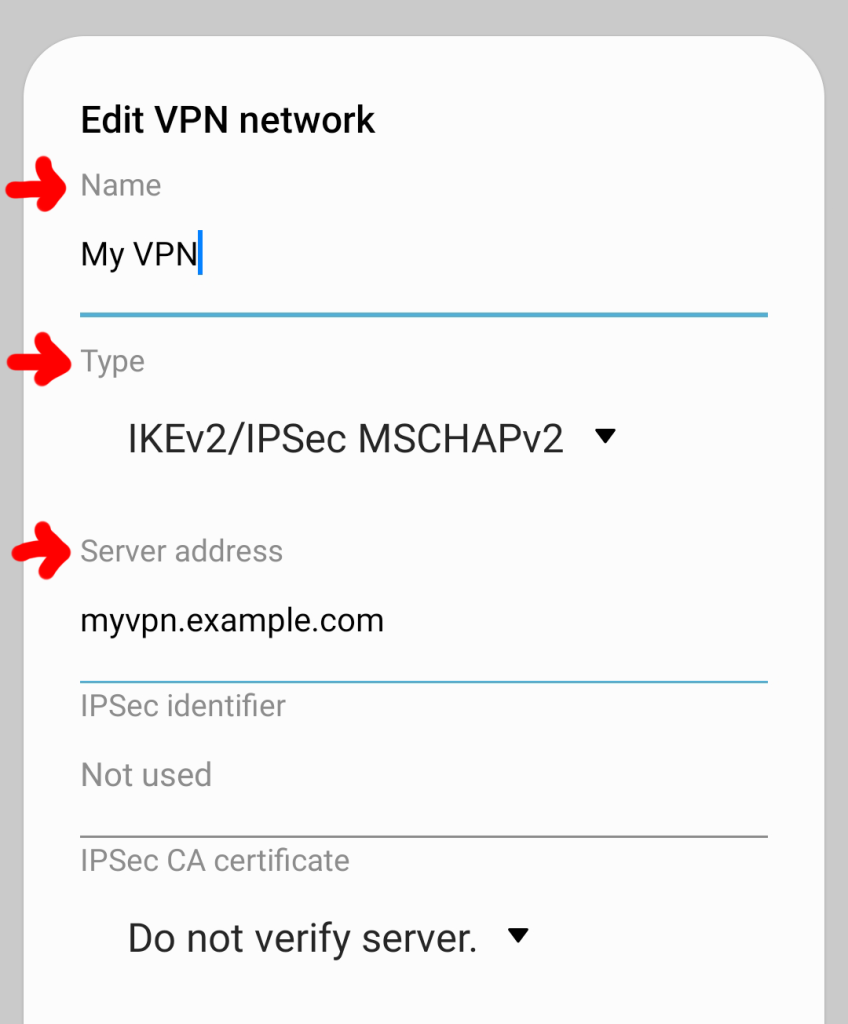
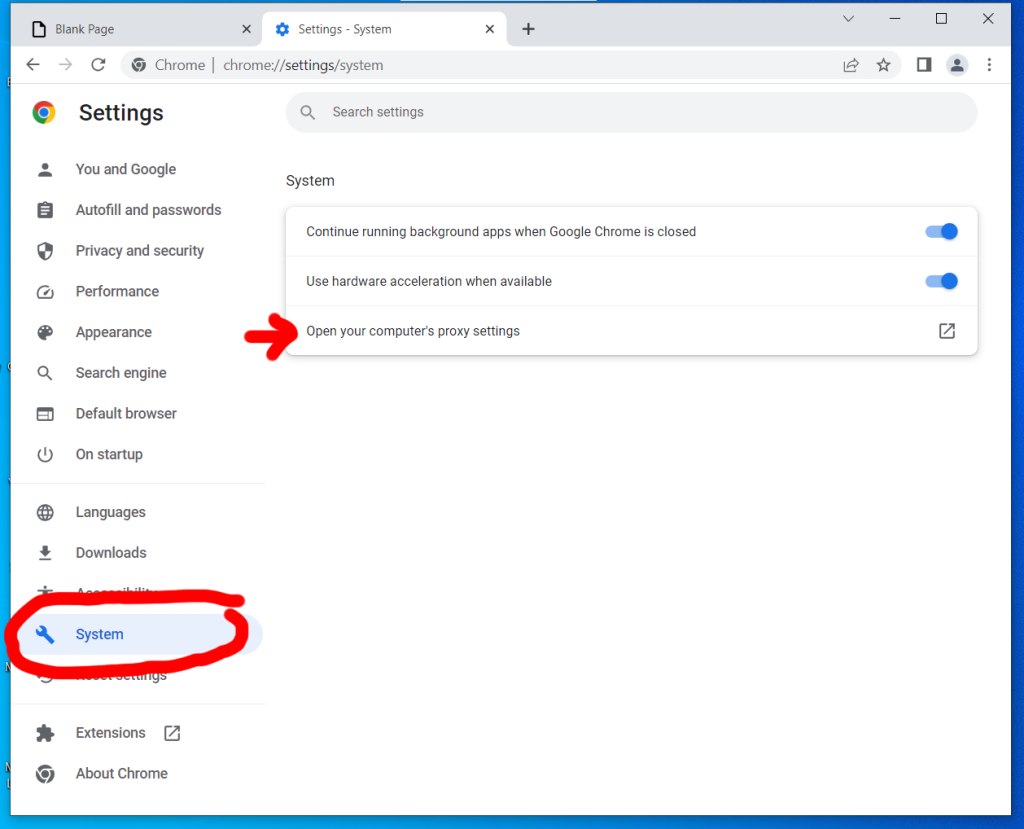
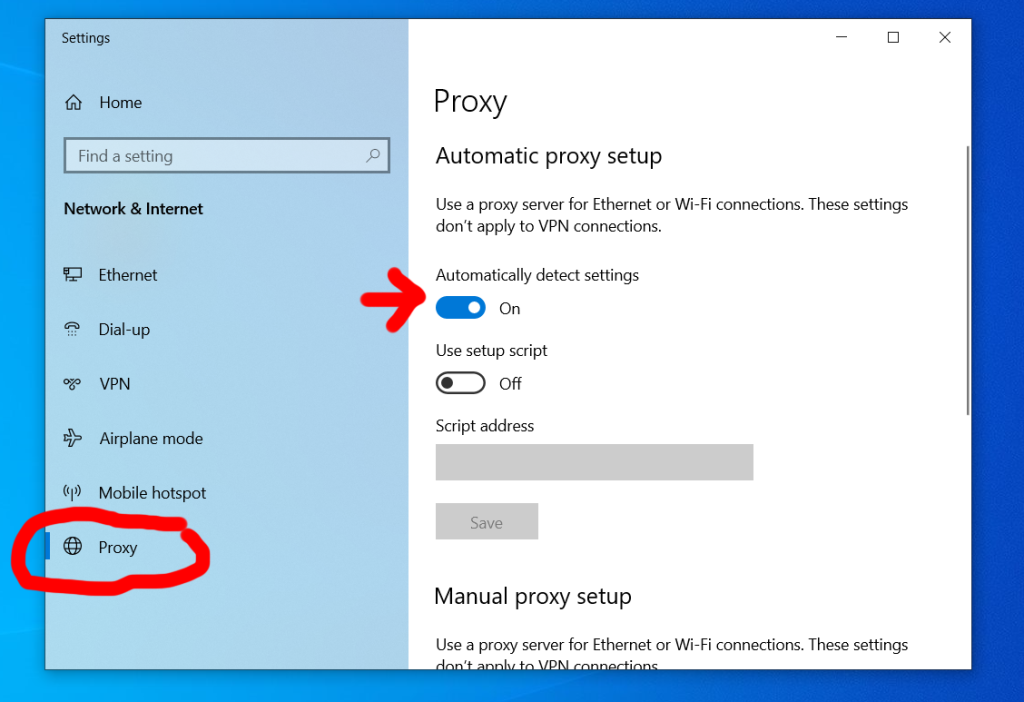
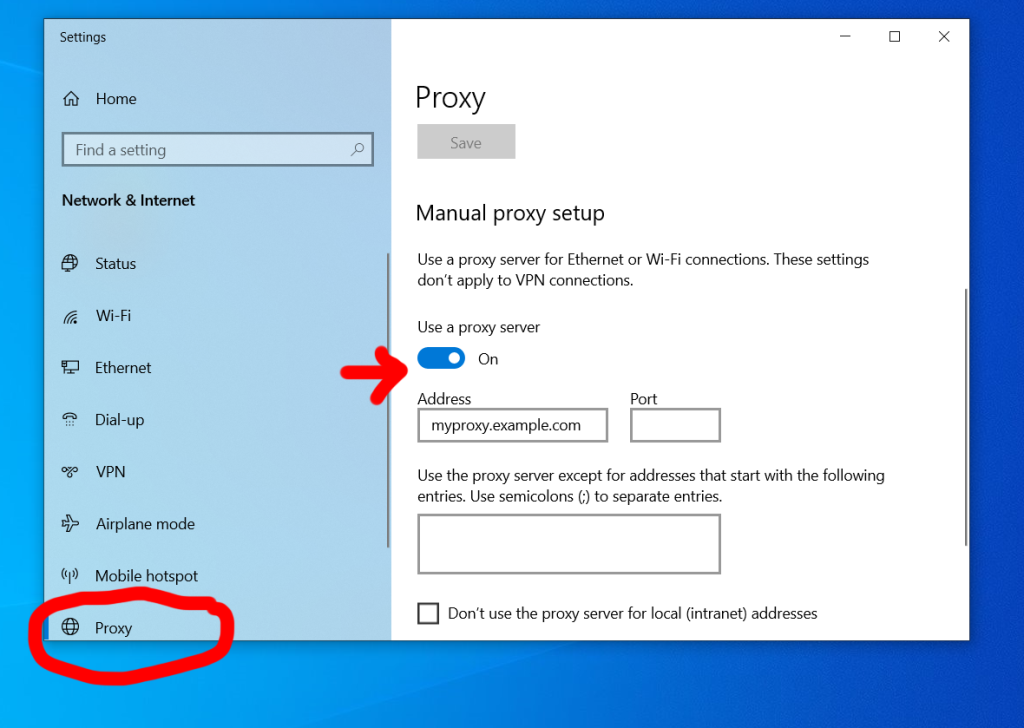
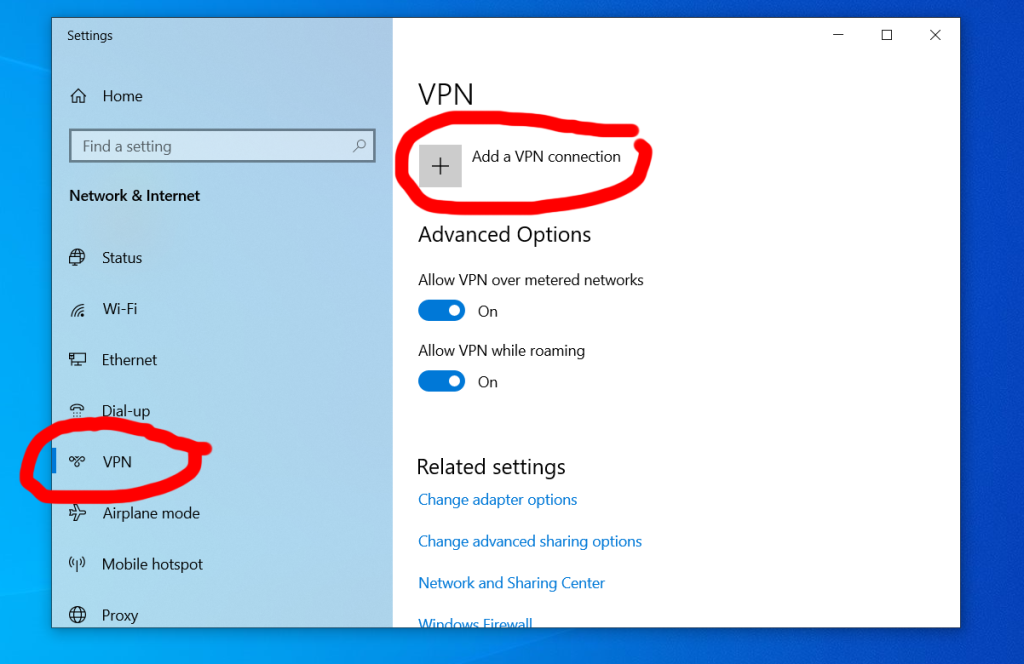
Use a VPN
VPNs create a secure tunnel in which all data flows between your internet connection and your gaming device.
Your real IP address is hidden and replaced with the IP associated with the VPN service. This makes it either difficult or impossible for companies and malicious users to pinpoint your location or gather data about you.
If you’re looking for a VPN, see LetMeBy’s top 3 VPN picks here. Alternatively, if you’re low on time, here are the VPNs most commonly recommended to gamers on this blog:
Avoid Using Cheats
Offering players cheats has become a common tactic used to trick unsuspecting gamers.
Here’s how it’s done.
Players looking for cheats and hacks will Google terms that bring them to an untrustworthy website. The site could use aggressive and misleading tactics to get players to click ads, complete surveys, or download malicious files.
Additionally, the cheat tool itself could use covert methods such as malware to obtain private data or it could use phishing to gain access to the gamer’s account.
Never download cheats as it not only goes against the terms of service in online games, it also puts your private data at risk. If you choose to download mods, do so from legit apps such as Steam or Epic Games and never from third-party websites.

Conclusion
Online gaming opens up incredible possibilities for players to compete and collaborate with other gamers, explore breathtaking environments, and acquire items that give their character a distinctive appearance.
It’s important to keep in mind that online games have greater risks as well.
There’s always a population of players looking for new ways to cheat and break the rules for their own gain. Online gaming has become so widespread that players are attractive targets for cybercriminals. On top of everything, many big gaming companies have become prying eyes.
Better online privacy doesn’t happen on its own. It’s something gamers need to strive for. And if you do, there’s a good chance your future self will thank you.














 Step 3
Step 3